
SAML (Security Assertion Markup Language) 2.0 SSO (Single Sign-On) minimizes the number of times a user has to login to various websites. It does this by having the user manually login to one site (called the identity provider or IDP) and then automatically logs the user into one or more other sites (called service providers or SPs), without having to provide credentials. A trust relationship must exist between the identity provider and the service providers, such that the Service providers trust that the identity provider has authenticated the user. SAML 2.0 supports two single sign-on flows:

In e-Business 6.0, we have built an Identity Provider which is IDP. This can work as an IDP for any Service Provider (SP). The Service Provider can be non-CMS or CMS, like Wordpress, Sitefinity, etc. which is SAML enabled. The Service Provider needs to send SAML based requests to e-Business 6.0, and it should be able to receive SAML response, process it and log in their system with the user information embedded in the SAML response.
Given below are the steps for this:
If already logged in, the IDP delivers the assertion or SAML response to the SP at the specified SPACS URL. This response contains user information like ID, name, email, and whichever field is configured in the stored procedure.
Under SAML configuration entity, we have an attribute called “IDPAttributesDataObject”. Corresponding to this, there’s a Stored Procedure, “spGetSAMLAssertionAttributes”. This SP returns some name/value pairs related to the person/web user. The result of this is embedded in the SAML Response sent by the IDP to the stored procedure. SP can utilize these field values as required. This stored procedure, as of now, returns first name, last name, and email. Also, it can be configured to return different results as per requirement. |
Suppose there’s another Service Provider SP2, which comes to IDP with Authn Request, and if the user is already logged in the IDP, the IDP directly sends the SAML Assertion to the SP2 without asking for user credentials.
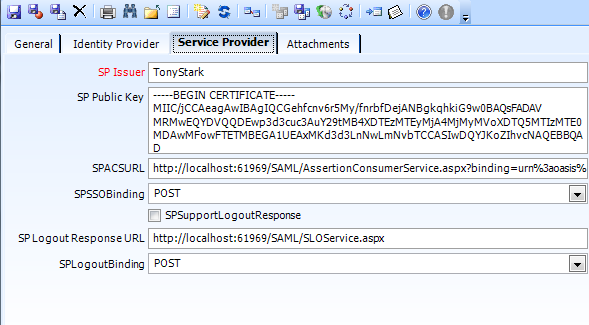
There are settings on smart client which the Administrator needs to do to configure SAML. To do this, follow the steps as given below:


Use below Public Key:
-----BEGIN CERTIFICATE-----
MIIF1zCCA7+gAwIBAgIJAO7bFs87n8vCMA0GCSqGSIb3DQEBCwUAMIGBMQswCQYDVQQGEwJVUzELMAkGA1UECAwCRkwxFzAVBgNVBAcMDlN0LiBQZXRlcnNidXJnMRgwFgYDVQQKDA9Db21tdW5pdHlCcmFuZHMxFDASBgNVBAsMC0Nyb3dkV2lzZG9tMRwwGgYDVQQDDBNDV19TQU1MX1NFTEZfU0lOR0VEMB4XDTIwMDQyMDE4MTA0N1oXDTQwMDQxNTE4MTA0N1owgYExCzAJBgNVBAYTAlVTMQswCQYDVQQIDAJGTDEXMBUGA1UEBwwOU3QuIFBldGVyc2J1cmcxGDAWBgNVBAoMD0NvbW11bml0eUJyYW5kczEUMBIGA1UECwwLQ3Jvd2RXaXNkb20xHDAaBgNVBAMME0NXX1NBTUxfU0VMRl9TSU5HRUQwggIiMA0GCSqGSIb3DQEBAQUAA4ICDwAwggIKAoICAQC/ymabmUzlziPRelAg7RuMhF/Oto7NLhm305oNK7kLlb6zYpuQv0POn0TBXJXOIL21VZIdFcDw8lfOCV1kja7WUYA7W7BUwd+4wtfDR4Kj3LNuTME3BjqU+C1sKvgFTko8wPi0iuagZkNuwDx3Zz6FGydGQxPVQZIilrT22HSp+pSxA4Ydb2ijY44waGnt2gI/NRsNx00rrWV0+H5FOd/l34ofLjm/fhuztYkiduxLjj8jXLrO41E0K0vY2V/mkhiJAnb8mg3xC+0RF2s1gamCEOyrUBK0I0pzZ1sDQEvleVrz/eA/bjUZJ9Sxa+VLqUxPjS+T5JHk9LGNAUsZEqaUmegy9RGMDQfq1cx9ZB9lmDBVRoh4i1EU39uHPWnf06sECuM3gHsBH3x9GxiQE5uX19t0fp0ZqIdcqm/eH9RYaza4lbU5ZoWTBnrMK07UEp7TDCQVDtn/c4LioBuLxB5FZXiBTYGC6dCKtjhjAP3FUCU6bteewA0xaRvdMdEUsBHtv8UDVq+duW27GGEEUGWJczAOUadaeAcj3oQFXv7Lpvmya1nwlmJx28fqkZ+AifIg6WsZBbPTLFctevOdjkzxBr9BYQC/a0AyNJbWDixqeEMU110qft/xYLeXT6vtz8043ZddzbA/1gotifurxezbgSfIT8EIX/2/qQXZZrqgLwIDAQABo1AwTjAdBgNVHQ4EFgQUtx6jFw9De0+3EAjez4McAyJfGpMwHwYDVR0jBBgwFoAUtx6jFw9De0+3EAjez4McAyJfGpMwDAYDVR0TBAUwAwEB/zANBgkqhkiG9w0BAQsFAAOCAgEAMUY6OJIzzH4C9DsZKYFkAGobFMGobK/UXA75+k9SIbU7PJ7iznoclEIu/2v31LAXVsLhrLGXs4NFt42H1ZQRAboKaXybC2/biRmkw3lYefeNL3vylbp14M54G3REayT4ZR8GVIxqW7c1eJ8Vb6Xpp5RC/UjajnwSMhnIw91Hj+d/Y3YXOMo+EfeYG5CakU8CE3oQV9csuVo2qS9rLZ8E6DiJtvO643b1HvhFrZax6waD/R+hn4IVB8jkoFSd/9zudNP6S11sj3k1Hu03Tvpd1H3npMJhFN8xMmLllenfMHM3ay2aV1szsJ18QLwz8dQTI55X1SsSxvGSrQwIeVfW9a/xRiYyc4jTR2fBmBC/Qnn8nAFNZevO8NKF3cAxKxBipuArj/qDCjcu/DSF327epayzaJbDO5OraUsYeYjqKCF74P7yw/2hbj6orWJJJKyhDaIsfzZsZX3cdlJfmc5/pqN7+SBjZRM8uo7DKFXqfkGgM152kVOz5fxW6Xz7TBKGC6dk2nm4tjpNxOItKABgpT+Lg2DhqUcmqoo4sEfdE1i1t88/CWB+W1EnenCbfE9HdR8A4ZV+wXbmYMGIfnUHUUHJ0wcIsbN8pkBNTmAsiil9tNBh4gBj7uiOcM61ZYcp321E0fU4QtJXWb6mkV9Ev3+V7xlU5iDlbmcvh1AXc5M=
-----END CERTIFICATE-----
4. Dump sp.pfx file into your website hosting path.
Following fields are not required:
|
For using Wordpress as SP, you need to turn off Anti Forgery, as the WP plugin doesn’t send CSRF tokens along with the requests. |








You do not need to maintain two login pages. SAMLLogin.html is a dummy SAML Login page shown above. You can make any other Login page (for example, Stock Login Page) SAML enabled, it just needs to submit(POST) to the SAML Endpoint which in this case is “{HostServicesURL}/v1/SAMLAuthentication” as shown in the image. It needs to send “Username”, “Password” as Post Data Parameters (In Body of request) and “Issuer” & “RelayState” as Query Parameters. It’s all shown in images above. |
So the POST URL would look as given below:
“{HostServicesURL}/v1/SAMLAuthentication?Issuer={yourIssuer}&RelayState={redirectURL}”
POST Data: {
"UserName": "username",
"Password": "pwd"
} |

This authenticates the user in IDP using the username, password and the issuer values provided in the request.

This receives SAML Authn Request using HTTP POST method and processes it.

This is responsible for logging out the user from IDP.



Wordpress SP Plugin Configuration (One Login SAML Wordpress Plugin – third party)
Local URL in Wordpress Environment (iw013192): http://localhost:81/wp/wp-admin/options-general.php?page=onelogin_saml_configuration




Follow the instructions given below to setup SAMPLE Service Provider .net Application for testing:
Open SAML2ServiceProvider project under ../SAML for .NET/Examples/SSO/LowLevelAPI/SP-Initiated/
<appSettings>
<add key="idpssoURL" value="https://xxxxx/SOA/v1/SAML/login"/>
<add key="idpLogoutURL" value="https://xxxxx/SOA/v1/SAML/logout"/>
</appSettings>
<!--Added Key for relayState, need to update as per requirement, or need to fetch from URL-->
<add key="relayState" value=[Your Redirect URL here]/>
where xxxxx is the IDP site.

Hosting on IIS:


IDP Side:
Refer idp.cer certificate file and copy it into your website hosting path, specify the full path of the Private Key File in the SAML configuration record under General Tab. The corresponding password should be updated in the Private Key Password field in SAML record.
Ideally, for SAML to work between e-Business 6.0 and classic controls on .net based CMS like Sitefinity, the CMS has to be SAML enabled, should be able to send/receive SAML messages. Sitefinity should use any SAML SP plugin, or we need to code for making the CMS SAML enabled. As of now, as a part of POC for SSO between classic and e-Business 6.0, we have used 2 Login, which means we login to both systems together.
For Wordpress mentioned previously, we have used SAML approach using one login SAML SP plugin. |
Below are points to look for, as per POC.



This hides the original button and new button is placed with same style and position as the original one. This new button, when clicked invokes the e-Business 6.0 login using the e-Business 6.0 Login JS code (Ajax call). On success, the original Login Button click event is fired which logs the user in classic as well.